Creating an Ansible Playbook
Introduction
In my previous post, I showed you how to prepare your Linux environment for the use of Ansible and the running of a basic test to ensure its functionality. Today's post will cover how to make use of this new setup with the introduction of Ansible playbooks, which you can read more in depth about here.
To summarize, Ansible playbooks allow you to bundle up various things, such as repeatable tasks or the configuration/management of a system, into a neat package, allowing for easy deployment as many times as you would like in the future. In today's post, we're going to start small by figuring out how we can use Ansible to automate the updates of our servers. While I'm aware that this could be done with functionality baked in to many Linux distros already, using tools like cron, I've been yearning for a project to familiarize myself more with Ansible and find use for it in my lab setup.
In my current situation when it comes to updating my servers, I am having to SSH into each of them and then manually run the typical sudo apt update and then sudo apt upgrade command. This has gotten to be a bit tedious with the amount of virtual machines I'm running at this point, hence the desire to find a way to automate things. I'd like to keep everything up to date to mitigate as many possible security vulnerabilities as I can.
With that being said, let's go ahead and get started
Creating the Playbook
Now that we're ready to create our first playbook, it's important to preface by noting that Ansible playbooks are written in YAML, so be sure you are careful with your tabs/spaces, as YAML is sensitive to them.
I'd also like to make note that all of my servers are currently running Ubuntu so we will be focusing on the apt module that Ansible provides.
With me having gone ahead and already created a "playbooks" directory for my playbooks to live in, I'm going to now create the file by running touch apt.yml. Now that it's created, you will want to open it up with the text editor of your choice and populate the file with the following contents:
- hosts: "*"
become: yes
tasks:
- name: apt
apt:
update_cache: yes
upgrade: 'yes'Let's break this down a bit, though:
To start, we have the first line specifying that we want this to apply for all hosts in our inventory file. We could also substitute the * with the attribute we've given to our servers, named ubuntu
Next, we have the line become: yes. become in this context is tied to whether we will be running this as a sudoer or not. With us having become set to yes, we're telling our playbook that we want to run this elevated privileges, something necessary to run our intended task.
Speaking of our task, we can take a look one line lower, where we now tell our playbook what we're wanting to do, which is using apt. Below that, we provide a couple of additional parameters, where we've told it to update cache and upgrade all of our modules.
If we take a look at the documentation for the apt module and specifically take a look at the upgrade attribute, we can see that we have several different options here:
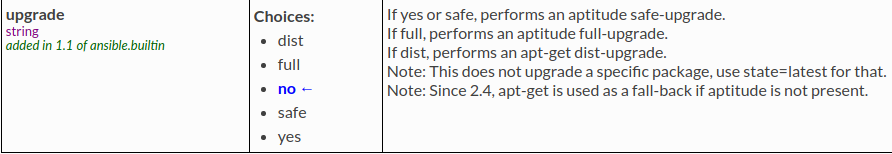
I've chosen the yes option because it's safer and does not perform a full dist upgrade. Your preference might differ here so feel free to choose what's applicable for your setup.
Using our Playbook
With the steps taken above, along with our inventory file created in the previous post, we are now ready to run our first Ansible playbook. To do so, we will now run the following command:
ansible-playbook /path/to/your/apt.yml --user (insert_user) --ask-pass --ask-become-pass -i /path/to/your/hosts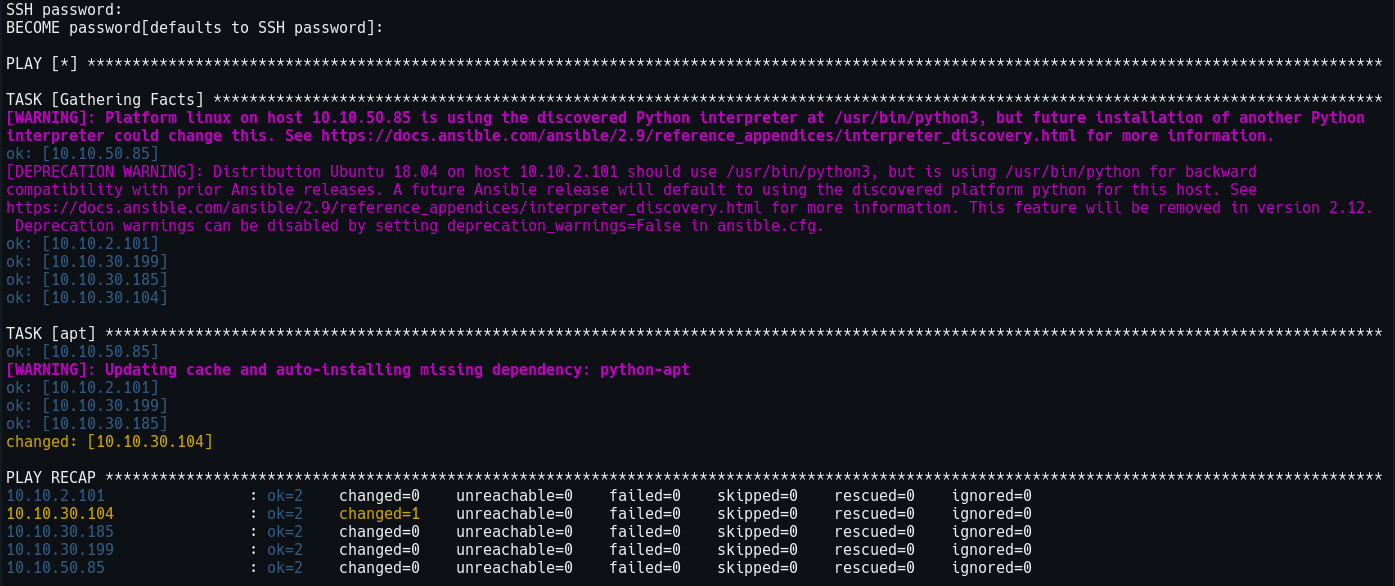
Provided you did not run into any serious issues, you should see something similar to the screenshot I have shown above. As you can see, I have a couple of warnings about Python versions but we're not going to worry about that right now.
Conclusion
As you can see, Ansible is a fairly easy tool to learn and utilize and makes your life easier by automating tasks for you. While we have just scratched the surface of Ansible's potential, I intend to keep you all updated on other neat ways I implement Ansible into my lab environment.
